Description
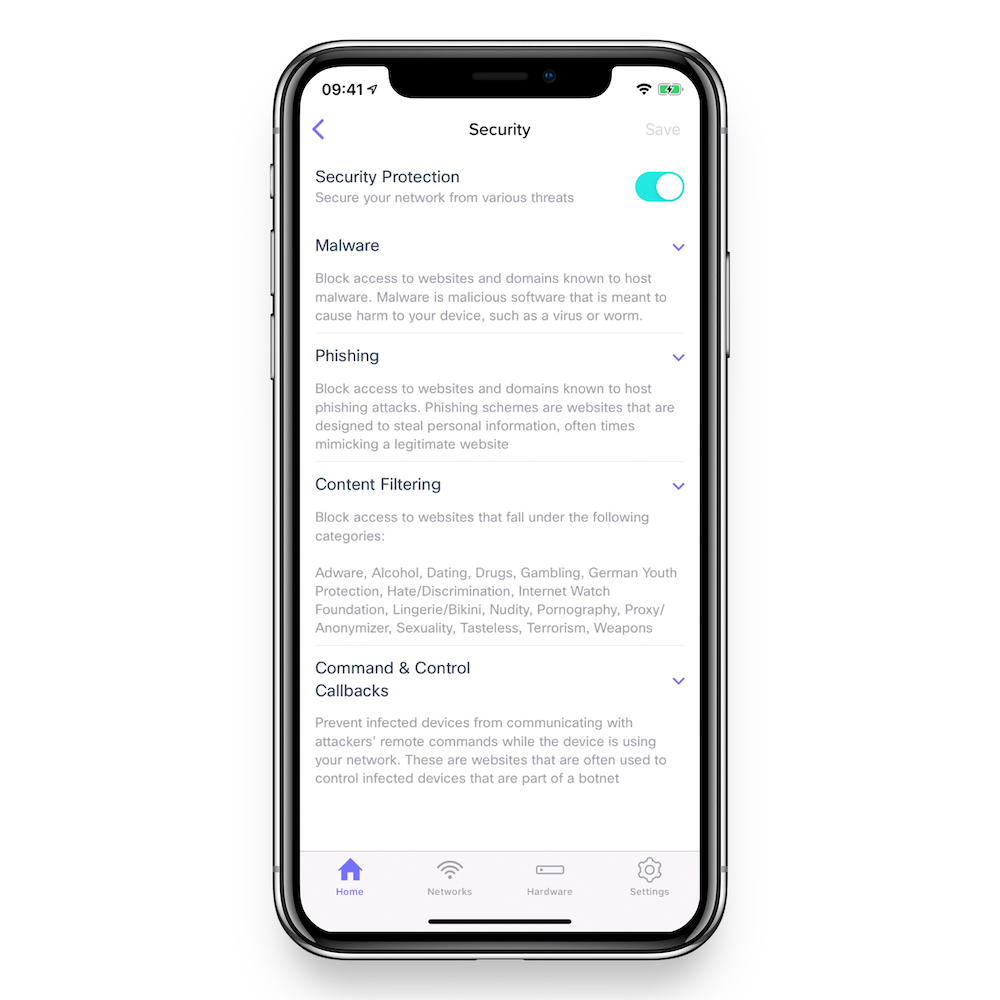
GX Security Settings
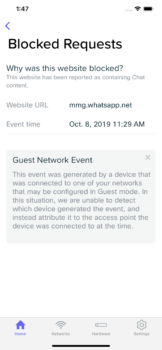
Each Meraki Go GX Security Gateway has an optional Security Subscription that can be purchased, powered by Cisco Umbrella. When this subsciption is purchased and applied, your Meraki Go GX Security Gateway can be enabled to use DNS based security measures to block certain types of traffic from your network.
What does it provide on top of the security already in the Meraki Go Security Gateway?
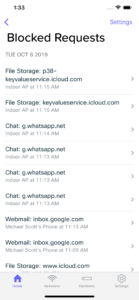
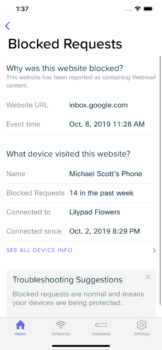
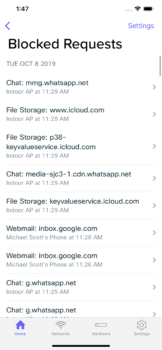
- Automatically reviews and blocks malicious sites
- Protects against attempts which could allow your network to be hacked
- Anti-phising
- Anti-malware
- Prevents hacker command & control communications (‘C2 Callbacks’)
- Single-tap Security Configuration
The above functionality is based on Cisco Umbrella which is cloud-delivered enterprise network security which provides users with a first line of defense against cyber security threats.